Difference between revisions of "MQP:Security Analysis Data Model"
From JimboWiki
(→Design) |
|||
| Line 33: | Line 33: | ||
**In order to make the structure easier to traverse, all classes that could be Results but also contain child results extend the abstract class ''ResultWithChildren'' | **In order to make the structure easier to traverse, all classes that could be Results but also contain child results extend the abstract class ''ResultWithChildren'' | ||
***ResultWithChildren provides a list of child results (of a specific type) and methods to add to the list, search the list, and create new children of the proper type | ***ResultWithChildren provides a list of child results (of a specific type) and methods to add to the list, search the list, and create new children of the proper type | ||
| + | |||
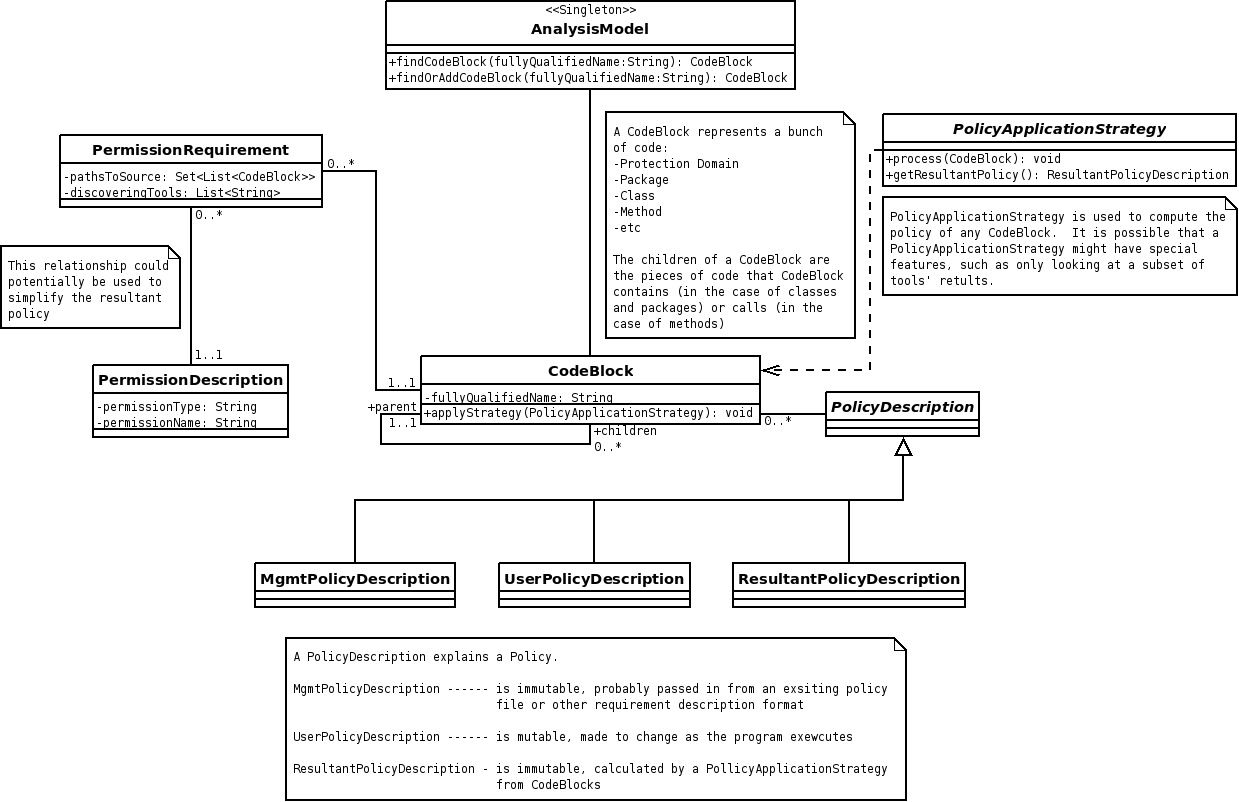
| + | [[Image:AnalysisModel.png|frame|left|Security Analysis Model]] | ||
Revision as of 19:10, 29 August 2008
Contents |
|
Overview
In order to provide the results of analysis, a data structure was devised to store the results.
Requirements
- The structure should be easy to traverse
- Mappings should exist between each security requirement and the block of code that the requirement applies to
- Levels of requirements should exist including:
- Method level requirements
- Class level requirements
- Protection Domain requirements
- The structure should provide a clear understanding of what permissions are "absolutely required" and "possibly required" for each code block
- Possibly Required - This permission is required under certain conditions, but not all conditions
- Absolutely Required - This permission is required under all conditions
- We can assume any permission that is not on either list of required permissions is not required under any condition
- The structure should provide a clear understanding of what permissions are "granted" and "denied" for each code block
- Granted - This permission is granted to the code block in the policy file
- Denied - This permission is explicitly denied in the policy file, or was denied during a runtime analysis
Design
- Data storage
- A top level singleton class, AnalysisModel, contains each result set
- The result set, ProgramAnalysisResult, contains sets of permissions for each class
- Each class's policy requirements are stored within the ProgramAnalysisResult as a ClassResult
- Each of the class's method's policy requirements are stored within the ClassResult as a MethodResult
- In order to record permission requirements, the PermissionDescription class is used to store the permission type and name
- Traversal
- In order to make the structure easy to implement and traverse, all classes that contain policy requirements extend the abstract class Result, which implements the following functionalities:
- Provide a name to the item that the policy requirements apply to
- Provide lists for each type of policy requirement (Possibly Required, Absolutely Required, Granted, and Denied)
- Provide methods to add permissions to each list
- In order to make the structure easier to traverse, all classes that could be Results but also contain child results extend the abstract class ResultWithChildren
- ResultWithChildren provides a list of child results (of a specific type) and methods to add to the list, search the list, and create new children of the proper type
- In order to make the structure easy to implement and traverse, all classes that contain policy requirements extend the abstract class Result, which implements the following functionalities: